Introduction
Defending cloud-native ecosystems requires more than just basic administration skills in today’s volatile digital landscape. Senior engineers must master the art of cluster hardening to protect sensitive data and maintain organizational trust. This comprehensive guide explores the Certified Kubernetes Security Specialist (CKS) Certification , a program designed to forge elite security practitioners. Professionals who seek to elevate their technical standing can find expert-led resources at DevOpsSchool to begin their journey toward mastery. By understanding the rigorous requirements of this track, engineering leaders and developers can build more resilient systems that withstand sophisticated modern threats.
What is the Certified Kubernetes Security Specialist (CKS) Certification Training Course?
The Certified Kubernetes Security Specialist (CKS) Certification Training Course functions as a rigorous validation of an engineer’s ability to secure containerized applications. It focuses heavily on the practical application of security principles across the entire software supply chain, rather than mere theoretical knowledge. This program forces candidates to think like attackers while building robust defenses that align with enterprise-grade production requirements.
In a modern engineering workflow, this certification represents the bridge between standard operations and advanced platform security. It emphasizes the “Secure by Design” philosophy, ensuring that every layer of the Kubernetes stack remains protected from external and internal risks. Professionals who complete this training understand how to navigate the complex intersection of networking, storage, and compute security within a dynamic containerized environment.
Who Should Pursue Certified Kubernetes Security Specialist (CKS) Certification Training Course?
Senior DevOps engineers and Site Reliability Engineers (SREs) who manage large-scale production clusters stand to gain the most from this certification. Platform engineers who build the foundations for developer self-service also find these skills essential for maintaining governance and compliance. Security architects transitioning into the cloud-native space use this program to translate traditional security concepts into the language of containers and microservices.
Engineering managers in India and across the globe prioritize this credential when hiring for high-stakes leadership roles. Even experienced cloud professionals who feel confident in their administration skills often discover significant knowledge gaps when they tackle the security-focused domains of this course. It serves as a definitive benchmark for anyone responsible for protecting the integrity and availability of organizational digital assets.
Why Certified Kubernetes Security Specialist (CKS) Certification Training Course is Valuable
The value of this certification stems from its focus on the fastest-growing sector of the infrastructure market: container security. As organizations migrate critical workloads to Kubernetes, the demand for specialists who can prevent breaches reaches an all-time high. Holding this credential signals to the industry that an engineer possesses the elite skills required to manage high-risk environments without compromising on speed or agility.
Beyond salary increases and career mobility, the program offers a massive return on investment by teaching long-term architectural patterns. These principles remain relevant even as specific tools evolve, giving professionals a lasting edge in a competitive job market. It empowers engineers to lead security initiatives, reduce the cost of breaches, and foster a culture of safety within their technical organizations.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification Overview
DevOpsSchool hosts and delivers the program through the Certified Kubernetes Security Specialist (CKS) Certification Training Course URL provided above. The exam utilizes a performance-based format, requiring candidates to solve complex security problems within a live, multi-cluster environment. This hands-on approach ensures that only practitioners with genuine technical competence can achieve the specialist status.
The Cloud Native Computing Foundation (CNCF) maintains the curriculum, ensuring it reflects the latest security challenges facing the industry. Candidates must demonstrate speed, accuracy, and deep technical intuition as they navigate various clusters to implement hardening measures. This ownership and structure guarantee that the certification remains the most respected technical validation for Kubernetes security experts worldwide.
Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification Tracks & Levels
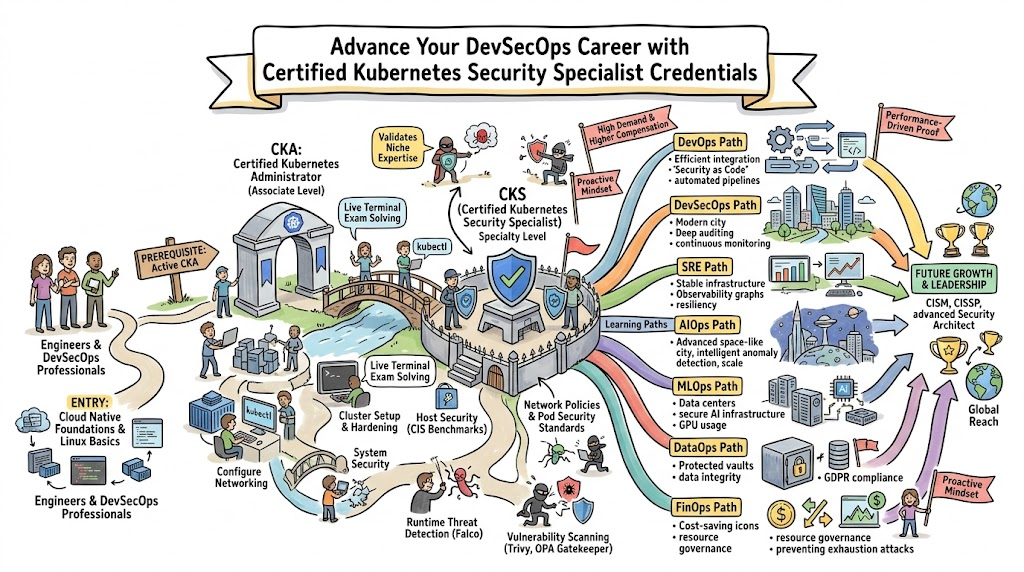
The certification journey begins at the foundational level, where engineers master the basics of containerization and cloud-native architecture. Success at this stage leads to the Associate level, which primarily focuses on the Certified Kubernetes Administrator (CKA) track. Candidates must hold a valid CKA certification as a non-negotiable prerequisite before they can attempt the security specialist exam.
Advanced tracks allow professionals to branch into specific engineering disciplines like DevSecOps or SRE specialization. Each level aligns with increasing responsibility in the workplace, moving from basic cluster maintenance to high-level security architecture. This structured progression ensures that every CKS holder possesses a rock-solid foundation in administration before they attempt to secure a production-grade cluster.
Complete Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Cloud Security | Foundational | Aspiring Engineers | Basic Linux | Containers, Security Basics | First Step |
| Administration | Associate | Cloud Admins | Foundational Cert | Cluster Ops, Networking | Second Step |
| Security Spec | Professional | Senior DevOps/SRE | Valid CKA Cert | Hardening, Supply Chain | Third Step |
| Platform Lead | Advanced | Engineering Leads | CKA + CKS | Governance, Multi-tenancy | Final Step |
Detailed Guide for Each Certified Kubernetes Security Specialist (CKS) Certification Training Course Certification
Certified Kubernetes Security Specialist (CKS) Certification Training Course – Certified Kubernetes Security Specialist
What it is
The CKS validates an individual’s proficiency in securing container-based applications and Kubernetes platforms during the build, deployment, and runtime phases. You prove your ability to harden environments and monitor for threats in a high-pressure, performance-based setting.
Who should take it
Experienced Kubernetes administrators who want to specialize in high-level security roles should pursue this track. It suits DevOps engineers, SREs, and security professionals who bear responsibility for the safety of production-scale container environments.
Skills you’ll gain
- You harden the cluster by configuring the API server, Kubelet, and ETCD securely.
- You implement sophisticated Network Policies to achieve micro-segmentation.
- You secure the container image supply chain using scanning and signing tools.
- You manage sensitive data through advanced Secrets management and encryption.
- You monitor runtime activity and detect anomalies using tools like Falco and Sysdig.
Real-world projects you should be able to do
- You audit an enterprise cluster and remediate all critical security misconfigurations.
- You build a secure CI/CD pipeline that automatically rejects vulnerable images.
- You configure a zero-trust network environment for a multi-tenant platform.
- You set up automated incident response triggers for unauthorized container access.
Preparation plan
- 7–14 days: You refresh your CKA knowledge and master the Kubernetes documentation structure to ensure rapid navigation during the exam.
- 30 days: You deep dive into image scanning, OPA Gatekeeper, and Falco, practicing each tool in a sandbox environment multiple times.
- 60 days: You complete full-length simulated exams, focusing on time management and precision in the command line interface to ensure success.
Common mistakes
- Candidates often ignore the CKA prerequisite, leading to basic administrative errors during the security tasks.
- Engineers frequently spend too much time on a single difficult question instead of moving forward to secure easier points.
- Many fail to practice with the specific versions of the third-party security tools mentioned in the exam curriculum.
Best next certification after this
- Same-track option: Advanced Cloud-Native Security Professional.
- Cross-track option: Certified Kubernetes Application Developer (CKAD) for a full-stack view.
- Leadership option: Certified Information Systems Security Professional (CISSP).
Choose Your Learning Path
DevOps Path
The DevOps path emphasizes the integration of security tools directly into the development cycle. You focus on creating automated guardrails that prevent insecure code or configurations from ever reaching production. This path creates a seamless experience for developers while maintaining high organizational safety standards.
DevSecOps Path
The DevSecOps path places security at the very center of the engineering culture. You specialize in “Shift Left” strategies, vulnerability management, and compliance-as-code. Professionals on this path often lead the technical implementation of security policies across the entire cloud-native organization.
SRE Path
The SRE path views security through the lens of system reliability and uptime. You focus on how security failures impact availability and how to build resilient systems that recover gracefully from attacks. This path involves deep work in monitoring, alerting, and automated incident response for security events.
AIOps Path
The AIOps path leverages machine learning to enhance cluster security at scale. You use intelligent algorithms to analyze vast amounts of log data and identify subtle patterns that indicate a security breach. This path suits engineers interested in the intersection of data science and infrastructure security.
MLOps Path
The MLOps path focuses on protecting the infrastructure that runs machine learning workloads. You secure the data pipelines and model training environments within Kubernetes. This path ensures that proprietary models and sensitive training data remain protected from unauthorized access or exfiltration.
DataOps Path
The DataOps path prioritizes the security of data processing engines and persistent storage. You master the art of securing databases on Kubernetes and ensuring that data at rest and in transit remains encrypted. This path is vital for organizations handling massive volumes of sensitive customer information.
FinOps Path
The FinOps path connects security configurations to cloud cost optimization. You ensure that security measures do not create unnecessary financial waste while maintaining a strong defense posture. This path requires a unique balance of technical security knowledge and financial accountability.
Role → Recommended Certified Kubernetes Security Specialist (CKS) Certification Training Course Certifications
| Role | Recommended Certifications |
| DevOps Engineer | CKA, CKS, Terraform Associate |
| SRE | CKA, CKS, Prometheus Expert |
| Platform Engineer | CKA, CKS, Cloud Architect (AWS/Azure) |
| Cloud Engineer | CKA, CKS, Linux Foundation System Admin |
| Security Engineer | CKS, OSCP, Certified Cloud Security |
| Data Engineer | CKA, CKS, Big Data Security Specialist |
| FinOps Practitioner | CKS, FinOps Certified Practitioner |
| Engineering Manager | CKS, ITIL, Project Management Professional |
Next Certifications to Take After Certified Kubernetes Security Specialist (CKS) Certification Training Course
Same Track Progression
Deep specialization after the CKS often leads engineers toward advanced container networking or specialized service mesh security certifications. These programs allow you to become the go-to expert for high-complexity environments where standard security measures are insufficient. You master the granular details of how traffic flows and how to protect the most sensitive microservices.
Cross-Track Expansion
Skill broadening involves mastering the developer side of the ecosystem by pursuing the CKAD (Certified Kubernetes Application Developer). You can also look toward mastering specific cloud providers like AWS or Azure at the professional architect level. This makes you a more versatile asset who understands how Kubernetes security interacts with the broader cloud infrastructure.
Leadership & Management Track
Transitioning to leadership requires a shift from technical execution to strategic risk management. Pursuing management certifications allows you to bridge the gap between deep technical security work and organizational business goals. You learn how to lead teams, manage budgets for security tools, and communicate risk effectively to non-technical stakeholders.
Training & Certification Support Providers for Certified Kubernetes Security Specialist (CKS) Certification Training Course
- DevOpsSchool provides a robust and immersive learning environment for those targeting the CKS credential. They offer live, instructor-led sessions that focus on the performance-based nature of the exam, ensuring students can execute tasks under pressure. Their curriculum stays updated with the latest CNCF standards, making them a top choice for professionals who need a structured and reliable path to certification.
- Cotocus specializes in high-end technical consulting and training for enterprise engineering teams. They offer intensive bootcamps that cover the deep technical domains of Kubernetes security, from kernel-level hardening to application-layer protection. Their focus on real-world production environments helps students gain the intuition needed to solve complex security puzzles that standard courses might overlook.
- Scmgalaxy acts as a comprehensive community resource and training platform for DevOps and security enthusiasts. They offer an extensive library of tutorials, practice labs, and mock exams specifically designed to mimic the CKS testing environment. Their platform is ideal for self-motivated learners who want to supplement their primary training with a wide variety of practical scenarios and community insights.
- BestDevOps focuses on delivering high-impact certification training that prioritizes exam readiness and practical skill acquisition. Their CKS program breaks down complex security topics into digestible modules, making it easier for busy professionals to master the material. They provide expert guidance on time management and exam strategy, helping students navigate the performance-based challenges with confidence.
- devsecopsschool.com dedicates its entire curriculum to the fusion of security and DevOps practices. Their CKS training program emphasizes the automation of security policies and the integration of vulnerability scanning into the CI/CD pipeline. This provider is perfect for engineers who want to lead the DevSecOps transformation within their respective organizations through technical excellence.
- sreschool.com approaches Kubernetes security from the perspective of system reliability and operational excellence. Their courses teach students how to build secure platforms that are also highly available and easy to maintain. By focusing on the intersection of security and SRE principles, they prepare engineers to manage the most mission-critical workloads in the cloud-native ecosystem.
- aiopsschool.com explores the future of infrastructure management by teaching students how to use AI to enhance cluster security. Their CKS training includes insights into automated threat detection and intelligent log analysis. This provider serves engineers who want to stay at the cutting edge of technology and use data-driven insights to protect their Kubernetes environments.
- dataopsschool.com focuses on the unique security challenges faced by data engineers running stateful workloads on Kubernetes. Their training covers persistent volume security, data encryption, and the protection of complex data pipelines. They provide the technical depth required to ensure that sensitive data remains secure throughout its entire lifecycle in a containerized world.
- finopsschool.com teaches engineers how to manage the financial side of Kubernetes security. Their courses help students understand the cost-benefit analysis of different security tools and how to implement a secure architecture that is also cost-effective. This provider is essential for senior engineers and managers who are accountable for both the safety and the budget of their cloud infrastructure.
Frequently Asked Questions (General)
1. Does the CKS exam require a lot of memorization?
The exam focuses almost entirely on your ability to execute tasks in a live environment rather than memorizing facts or definitions.
2. How many hours should I dedicate to CKS labs each week?
Success usually requires at least 10 to 15 hours of hands-on lab practice per week over a two-month period for most candidates.
3. What happens if my CKA certification expires before I take the CKS?
You must maintain an active CKA certification to be eligible to take the CKS exam, so ensure you renew it if necessary.
4. Can I use a Mac or Windows machine for the exam?
You can use any machine that supports a modern web browser, as the exam takes place in a remote terminal environment.
5. How quickly do I receive my exam results?
The Linux Foundation typically releases exam results via email within 24 to 36 hours after you complete the test session.
6. Are there specific browser extensions I need for the exam?
The exam environment usually requires you to disable most extensions and may require a specific proctoring plugin for your browser.
7. Does the exam include questions on Windows nodes?
The current CKS exam focuses exclusively on Linux-based clusters and nodes, which represent the majority of production Kubernetes environments.
8. Is the CKS more valuable than the CKAD?
The CKS is generally considered more advanced and carries a higher market value for infrastructure and security-focused roles.
9. Can I skip questions and come back to them later?
You can navigate between questions freely, and it is a recommended strategy to skip difficult tasks and return to them if time permits.
10. What is the best way to practice for the performance-based tasks?
The most effective method involves setting up your own multi-node cluster on a local machine or cloud provider and breaking things on purpose.
11. Does the exam cover cloud-provider-specific security tools?
The exam focuses on platform-agnostic tools and Kubernetes native features that work across any cloud or on-premises environment.
12. How often does the CKS curriculum change?
The curriculum undergoes regular updates to stay aligned with the latest Kubernetes releases and the evolving landscape of cloud-native threats.
FAQs on Certified Kubernetes Security Specialist (CKS) Certification Training Course
1. Does the training include practice with OPA Gatekeeper?
The course provides detailed modules on implementing and testing Open Policy Agent (OPA) policies to enforce organizational governance within your clusters.
2. Will I learn how to secure the Kubelet and API Server?
You will master the specific flag configurations and authentication methods required to harden the core components of the Kubernetes control plane.
3. Does the curriculum cover container image signing with Cosign?
The training includes practical labs on verifying image integrity and ensuring that only signed, trusted images can run in your production environment.
4. How does the course handle runtime security monitoring?
You use tools like Falco to create custom rules that alert you to suspicious system calls or unauthorized file access within your containers.
5. Is mTLS and Service Mesh security part of the CKS training?
The course covers the fundamentals of mutual TLS and how service meshes can enhance the security of communications between your microservices.
6. Will I learn about gVisor and container sandboxing?
You will explore how to use alternative container runtimes like gVisor to provide stronger isolation for high-risk workloads in a shared cluster.
7. Does the training explain how to use Kube-bench and Kube-hunter?
The curriculum teaches you how to use these automated tools to scan your clusters for common vulnerabilities and CIS benchmark compliance.
8. Are Network Policies covered in depth during the labs?
You will spend significant time building and troubleshooting complex Network Policies to restrict traffic and protect sensitive pod-to-pod communication.
Final Thoughts: Is Certified Kubernetes Security Specialist (CKS) Certification Training Course Worth It?
Investing in the Certified Kubernetes Security Specialist (CKS) Certification Training Course represents a strategic move for any engineer serious about their future in cloud technology. As the industry moves away from basic deployments and toward complex, high-security architectures, those who can prove their expertise will lead the pack. The program forces you to confront the reality of modern threats and gives you the technical toolkit to build defenses that actually work in production.
Choosing this path demonstrates a commitment to technical excellence and a deep understanding of the responsibilities that come with managing enterprise infrastructure. While the journey to certification is demanding, the knowledge you gain becomes a permanent part of your professional identity. For those ready to move into the upper echelons of the DevOps and security world, this certification provides the most direct and respected route to success.
Leave a Reply